Conclusion to Understanding Cyber Threats Training
Review the key concepts and strategies discussed throughout the course, emphasizing the importance of continuous education and adaptation in the world of cybersecurity.
The Future of Cyber Threats and Defense
As technology advances, so do cyber threats. Understanding the dynamic nature of these threats and the importance of staying updated with the latest security trends and practices is crucial for effective cyber defense.

Reflecting on the key learnings from each module, revisit the essential points covered in the training, reinforcing the critical aspects of cyber threat awareness and defense.
A crucial takeaway is the ability to recognize various cyber threats, including phishing, malware, ransomware, and social engineering attacks. Understanding these threats is the first step in mitigation. Implementing strong password policies, regularly updating software, and maintaining robust firewall and antivirus systems are fundamental practices.
Proactive cybersecurity measures are essential in preventing attacks before they occur. This involves not only technological solutions but also strategic planning. Regular vulnerability assessments and penetration testing can identify potential weaknesses in the system. Establishing an incident response plan ensures a swift and organized reaction to any security breaches. Investing in cybersecurity is not an overhead but a crucial aspect of business continuity and reputation management.
Empowering employees through knowledge and action is a key defense strategy against cyber threats. This involves comprehensive training programs that cover not only the technical aspects of cybersecurity but also the behavioral changes required to enforce security policies. Encouraging a culture of openness, where employees can report suspicious activities without fear of reprimand, is important. Regular updates and refresher courses on cybersecurity best practices help maintain vigilance.
Maintaining Vigilance and Adaptation in Cybersecurity
Cybersecurity is an ongoing process that requires constant vigilance and adaptation. Here are some tips on maintaining a robust defense against future cyber threats.
Here are some myths to look out for:
- -
Staying informed about emerging cyber threats and trends
- -
Regular training and updating of cybersecurity skills
- -
Implementing and updating cybersecurity policies and protocols
- -
Encouraging a culture of security within organizations
- -
Engaging in continuous monitoring and improvement of security systems

Continuous education is key to combating Cyber Threats
Remember that cybersecurity is a continuous journey. By applying the knowledge and strategies acquired from this course, your employees will be better equipped to face current and future cyber threats. Keep advancing your cybersecurity skills and awareness to protect your digital assets and maintain a secure online presence.

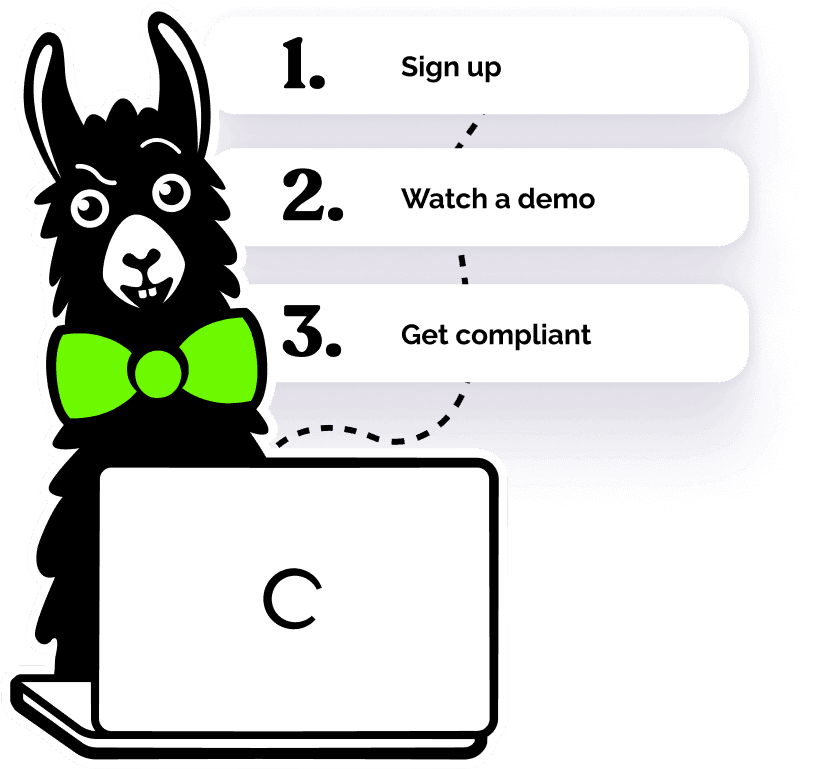
Helping over 8,000+ organizations create a safer, more inclusive company culture
The goal of this training is to provide employees with essential knowledge and skills to effectively understanding cyber threats in the workplace, ensuring a safer environment for everyone. This course covers: