Introduction to Understanding Cyber Threats Training
From understanding malware to recognizing social engineering tactics, this course prepares you to navigate the digital landscape securely, protecting both personal and professional data.
Differentiating Between Safe and Risky Online Practices
Distinguishing between safe and risky practices is vital for cyber safety. This involves being aware of the tell-tale signs of phishing, understanding the risks associated with unsecured networks, and recognizing the dangers of sharing personal information online.

The expansion of Internet of Things (IoT), which refers to the collective network of connected devices and the technology that facilitates communication between devices and cloud, has brought new challenges in cybersecurity. Here are some strategies and practices essential for protecting these devices from emerging cyber threats.
Securing IoT devices involves implementing robust security protocols to protect against unauthorized access and data breaches. This includes regular firmware updates, employing strong encryption methods for data transmission, and setting complex passwords.
Safeguarding mobile devices is critical in a world where they are integral to our daily lives. This includes installing reliable security software to guard against malware and phishing attacks. Regularly updating operating systems and applications to patch security vulnerabilities is essential. Educating users about the risks of unsecured Wi-Fi networks and the importance of using strong, unique passwords for each application is also key.
Network security for IoT and mobile devices focuses on protecting the data transmitted across networks and preventing unauthorized access. This entails using secure communication protocols, like VPNs, and segmenting networks to isolate sensitive data and devices. Firewalls and intrusion detection systems should be employed to monitor and control incoming and outgoing network traffic
Essential Strategies for Mitigating Cyber Threats
Protecting yourself from cyber threats involves a combination of knowledge and practical steps. Here are some essential strategies to help you stay safe in the digital world.
Here are some myths to look out for:
- -
Regular software and security updates
- -
Strong, unique passwords for all accounts
- -
Caution with email attachments and links
- -
Secure network connections
- -
Regular backups of important data

Empower Employees with Cybersecurity Knowledge
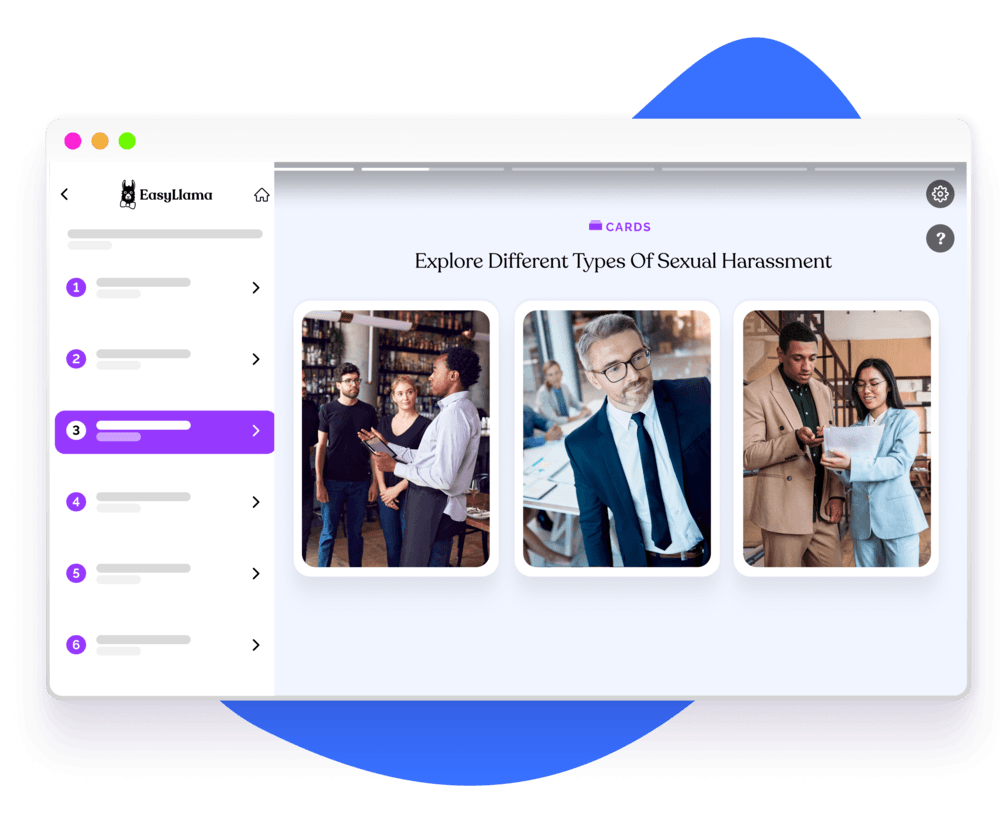
Our course, filled with live-action video and interactive modules, offers the knowledge and practical skills you need to protect yourself and your organization from digital threats. Stay one step ahead in the ever-evolving world of cyber security.

Helping over 8,000+ organizations create a safer, more inclusive company culture
The goal of this training is to provide employees with essential knowledge and skills to effectively understanding cyber threats in the workplace, ensuring a safer environment for everyone. This course covers: