Physical Cybersecurity Threats
Physical threats involve direct interactions with hardware or physical breaches of security protocols. Understanding and mitigating risks such as USB drops, hardware keyloggers, and dumpster diving are crucial for comprehensive cybersecurity.
The Risk of USB Drops
The risk of USB drops, a method where USB drives containing malware are left in public or corporate spaces, poses a significant cybersecurity threat. When unsuspecting individuals find these drives and connect them to their computers, the malware automatically installs, potentially giving cybercriminals unauthorized access to sensitive data and systems. This technique exploits human curiosity and the apparent harmlessness of a lost USB drive, making it a deceptively simple yet effective tool for spreading malicious software.

Physical cybersecurity threats can take various forms, each requiring specific awareness and preventive measures. Let’s focus on understanding these diverse threats and how they can compromise security.
USB drops, where USB drives are left in public places, pose a significant security risk. These drives may contain malicious software designed to infect a computer once connected. To mitigate this threat, organizations should enforce policies against using found USB devices and educate employees about the risks. Using antivirus software that scans USB drives upon insertion and restricting USB access on sensitive systems can also be effective measures.
Hardware keyloggers are devices covertly installed between a keyboard and a computer to record keystrokes, potentially capturing sensitive information like passwords and confidential data. To combat this threat, regular physical inspections of computer hardware are essential, particularly in high-security areas. Educating employees on recognizing unfamiliar devices attached to their workstations is also vital.
Dumpster diving involves searching through a company’s waste to retrieve sensitive information that hasn’t been properly disposed of. To address this threat, companies should implement strict policies for disposing of sensitive materials, including shredding documents and destroying old storage media. Educating employees about the importance of proper disposal practices is also critical.

Hardware Keyloggers: A Stealthy Threat
Hardware keyloggers, devices physically attached to keyboards or hidden within them, record every keystroke made by a user. This information can include sensitive data like passwords, credit card numbers, and personal messages. The insidious nature of hardware keyloggers makes them particularly dangerous, as they can operate undetected for extended periods. Awareness of these devices, regular physical inspections of hardware, and secure handling of sensitive information are key measures in safeguarding against this type of intrusion.
Preventive Strategies Against Physical Cyber Threats
Addressing physical cybersecurity threats requires a mix of vigilance, policy enforcement, and secure practices. Explore key preventive strategies to protect against such physical intrusions.
Here are some myths to look out for:
- -
Regular security audits and physical inspections
- -
Secure handling and disposal of sensitive documents and storage media
- -
Awareness training for employees on identifying and reporting potential physical threats
- -
Implementing strict access controls to sensitive areas
- -
Encouraging a culture of security mindfulness among staff

Strengthen Your Company’s Defense Against Physical Cyber Threats
Heighten your employee’s awareness and preparedness against these often-neglected risks. By understanding the nature of these threats and adopting comprehensive protective measures, you can significantly bolster the overall security posture of your organization against physical cyber intrusions.

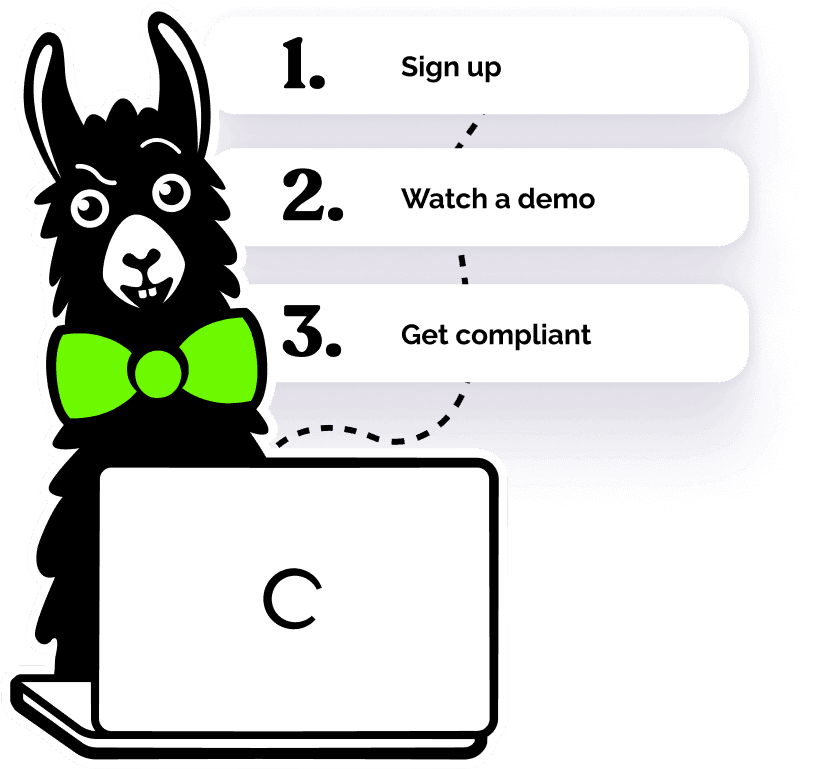
Helping over 8,000+ organizations create a safer, more inclusive company culture
The goal of this training is to provide employees with essential knowledge and skills to effectively understanding cyber threats in the workplace, ensuring a safer environment for everyone. This course covers: